Target, Sony, and the Democratic National Committee have been victims of cyber security attacks and data theft. And while these attacks have had a negative impact on customers, employees, and political candidates, the fact remains: sophisticated criminal organizations, foreign governments, and hacktivists are exploiting cyber security vulnerabilities with greater frequency and effect.
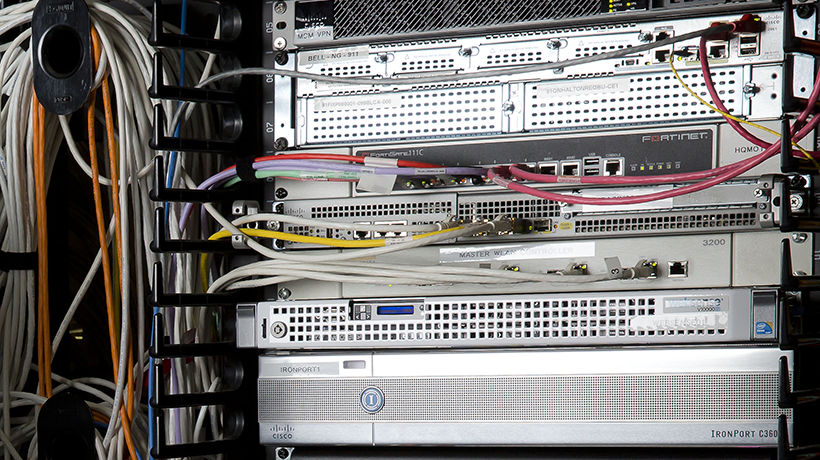
At its basic level, cybersecurity measures are designed to protect IT environments and solutions from intrusions and viruses that may cause theft or corruption to sensitive or critical data. In the case of law enforcement and public safety agencies, computer-aided dispatch systems and records management systems could be the focus of cyberattacks. Consider how stolen information about police officers could make them targets for ISIS operatives or how ransomware could render a CAD system unable to dispatch critical resources during a crisis event. While those scenarios are hypothetical, they are highly possible given the growing threat of cyber attacks against agencies and organizations of all types.
Luckily for law enforcement and public safety agencies, there are cybersecurity requirements mandated by the Federal Bureau of Investigations’ Criminal Justice Information Services (CJIS) division. CJIS requires agencies to have systems locked down and implement certain protocols for password protection, intrusion detection, intrusion response, and more. For next-gen 911 and communications, the Federal Communications Commission (FCC) is mandating I3 standards because next-gen 911 and communications technologies are all IP-based.
Given the need to comply with CJIS and FCC cybersecurity requirements, here are a few best practices that federal, state, and local public safety agencies can use to ensure better security of IT environments and systems.
Developing Well-defined Policies
Some agencies have strong cybersecurity policies in place while others don’t. This is an area that can be improved upon and better defined. An agency needs to develop risk-based policies, meaning that it should look at vulnerabilities and gauge the risk against what types of functionalities it’s willing to lose when policies are implemented. And that is a balance. Agencies don’t want to lock down systems and it make it difficultfor users, but it’s also important want to protect the system from vulnerabilities and threats. Once cybersecurity policies are defined, it’s critical to educate everyone within the agency as well as enact the policies agency-wide.
Creating a Schedule for System Protection
While this sounds simple, it’s actually a lot of work. Protecting an IT environment requires downloading and implementing software patches and updates on a regular basis. Those patches could be for Microsoft Windows Server OS, a Hexagon solution, or another software technology all together. Once the patches are done, anti-virus software needs to be updated and scanning the system on a regular basis. To do patching and system scanning effectively, agencies need to create a schedule to perform these critical tasks. Within that schedule, an agency should also define how often it monitors its systems for hacks. And if an agency sees intrusions, they should know what the protocol is to respond and react to cyber threats.
Responding and Reacting to Cyber Threats
While not required for state and local public safety agencies, defining response and reaction steps in a cybersecurity policy is beneficial. A good place to start researching requirements would be the National Institute of Standards and Technology’s Risk Management Framework (RMF). Used by federal government agencies when creating cybersecurity policies, the RMF provides guidance for responding and reacting to cybersecurity attacks and how to lock down a system with secret and top secret information among other things. The RMF is also a great resource for comparing CJIS requirements and the FCC’s I3 standards when an agency is creating a cybersecurity policy.
The benefit of using Hexagon Safety & Infrastructure’s Intergraph Computer-Aided Dispatch system and other public safety technologies is that our solutions were created with CJIS, FCC, and RMF compliance in mind. Our product managers and solution engineers understand the ever-growing and evolving nature of cybersecurity policies – and threats. If you would like to know more about cybersecurity issues and best practices with regard to our public safety solutions, please email me.